AMD Processors Manufactured Between 2011 And 2019 Are Vulnerable To 2 New Attacks
newsMonday, 09 March 2020 at 15:14
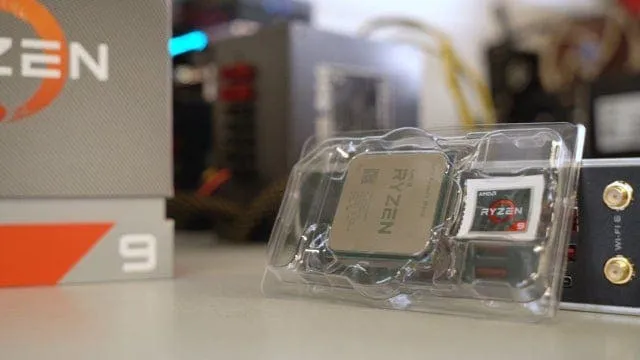
A study released this week showed that AMD processors produced between 2011 and 2019 are vulnerable to two new attacks. These two new attacks affect the security of data processed inside the CPU, leading to the theft of sensitive information or degraded security features.
Also read: AMD Dominates The Charts Of Best-Selling Desktop Processors
The research team stated that they had notified AMD of these two issues in August 2019. Бut AMD did not release microcode (CPU firmware) updates and claimed that these were ‘not new speculative-based attacks’ and the research team did not аgree with this statement.
What Kind Of Attacks May Hurt AMD Processors?
The predictor computes a μTag using an undocumented hash function on the virtual address. This μTag is used to look up the L1D cache way in a prediction table. Hence, the CPU has to compare the cache tag in only oneway instead of all possible ways, reducing the power consumption.
The two new attacks were discovered after a team of six academics -- from the Graz University of Technology in Austria and the Univerisity of Rennes in France -- reverse-engineered this "undocumented hashing function" that AMD processors were using to handle μTag entries inside the L1D cache way predictor mechanism.

Тwo new attacks they found were the Collide + Probe attack and Load + Reload. These two attacks are somewhat similar to the classic Flush + Reload and Prime + Probe attacks. These attacks were used by other researchers in the past to leak data from Intel processors, but not AMD processors. The way the AMD processors process data is cached is different from Intel processors. In simple terms, these two attacks can be used to monitor how a process interacts with the AMD cache. Then, they will leak some data from other applications.
AMD denies that these two new attacks are worrisome. It also claims that the attacks are ‘not new speculative-based attacks’ and that these attacks should be mitigated by previous Speculative_execution side-channel vulnerability fixes. But the above research team described AMD's response as ‘quite misleading’. After the initial report of the vulnerability last August, AMD has never contacted their team. And the attack can still be performed on brand new operating systems, firmware and software.
Popular News
Latest News
Loading



