Cyberark security researchers are warning from the resurgence of the banking malware Raccoon. The latter is enjoying growing popularity on hacking forums. It can steal banking and crypto-currency data by exploiting flaws in Chrome, Edge, Firefox… – more than 35 browsers and 60 applications in total, including email clients. The services of this malware are rented on the dark net.
This malware first discovered in 2019 is like Cerberus, a malware as a Service (MaaS). In other words, a malicious program whose users hire the services with a complete package, available from $200 per month. And this is one of the reasons to fear it right away: anyone can indeed use it for a fee.
Raccoon malware: 35 browser and 60 programs affected
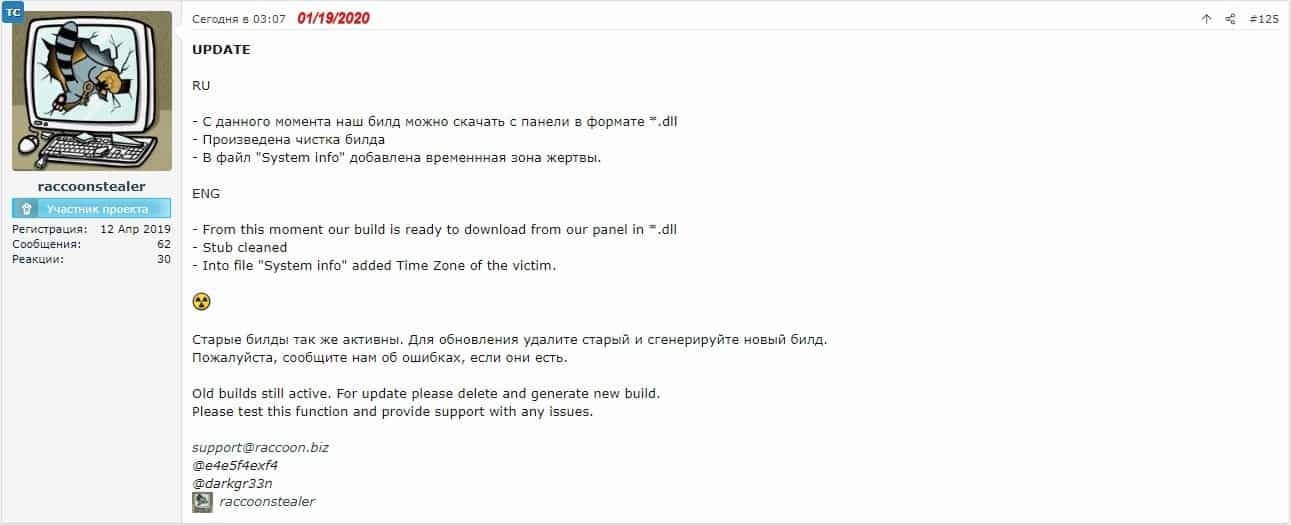
The hackers who maintain it provide a protected hosting space for the control server, with an intuitive interface. But also technical support and regular updates. At this price, it is not the cheapest option for beginner pirates, but Cyberark researchers note that it is the simplest and most complete. Especially since this banking malware is more sophisticated than the other examples detected in nature. Raccoon can indeed exploit vulnerabilities in 35 browsers and 60 programs in total, including:
- Google Chrome
- Chromium
- Xpom
- Comodo Dragon
- Amigo
- Orbitum
- Brom
- nichrome
- RockMelt
- 360Browser
- Vivaldi
- Opera
- Sputnik
- Kometa
- Uran
- QIP Surf
- Epic Privacy
- CocCoc
- CentBrowser
- 7Star
- Elements
- TorBro
- Suhba
- Safer Browser
- Mustang
- Superbird
- Chedot
- Torch
- Internet Explorer
- Microsoft Edge
- Firefox
- Waterfox
- SeaMonkey
- PaleMoon
- Thunderbird
- Outlook
- Foxmail
The main factor of infection is phishing campaigns and exploit kits. Malicious e-mails generally contain an attachment, often an office document containing a malicious macro. Once launched, the malware copies the files containing sensitive data (mainly access to cryptocurrency wallets, cookies, history and autofill content) to a temporary folder, then extracts and decrypts the data before sending it to the so-called “Control and command server”.
Researchers say the malware can easily steal crypto from the following wallets: Electrum, Ethereum, Exodus, Jaxx, Monero, and Bither. Development around Raccoon remains very active. So that there is not necessarily an effective method of protection, except to be particularly wary with emails with attachments. A complete analysis of the malware and its risks is available on the Cyberark website (source).





