Over the past month, the number of malicious campaigns that in any way exploit the theme of COVID-19 is increasing. Now, experts have noticed a malware that can steal and destroys data from affected users and overwrites the MBR (Master Boot Record), which prevents the system from starting normally.
ZDNet has reported that security researchers have managed to identify at least five malware strains that affect Windows PCs, some distributed in the wild, while others appear to have been created only as tests or jokes.
This COVID-19 malware can steal your data and erase your entire hard drive
Four of these are dangerous, they exploit the theme of Coronavirus, as well as focus on the destruction of information, rather than financial gain. Of the four malware specimens discovered by IB researchers last month, the two most advanced were those rewriting MBR.
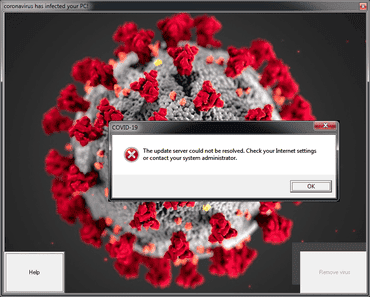
So, the first one was discovered by MalwareHunterTeam and described in detail in this week’s SonicWall report. This malware spreads as COVID-19.exe file and has two stages of infection.
At the first stage, the malware simply shows an annoying window that users cannot close, since the malware has already disabled the Windows task manager. But while users try to figure out how to close the window, the malware damages the MBR, and then reboots the PC. As a result, the user can not access his PC, and the system does not boot beyond the preload screen. Fortunately, in this case, it is possible to restore access to the machine and data. For this, you will need special software to restore the MBR.
MBR-REWRITING MALWARE
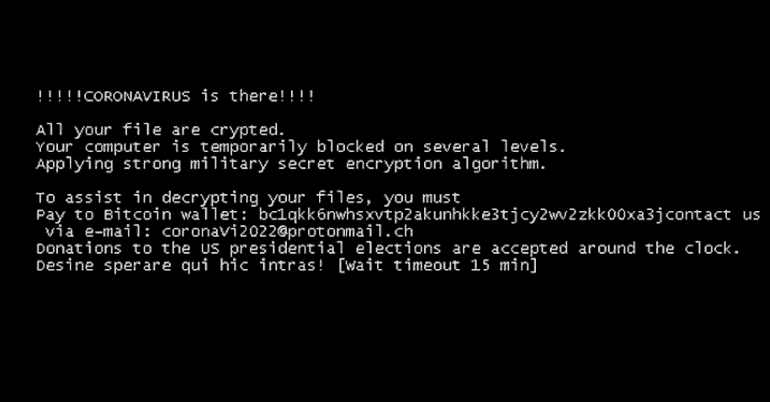
The second strain of “coronavirus” malware also rewrites MBR, but it looks more complicated. At first glance, this is just another ransomware who’s name is “CoronaVirus” but this is just a cover. The main function of this malware is to steal your passwords. And then imitate extortion activity, designed to hide the real state of affairs from the victim.
The fact is that as soon as CoronaVirus has stolen the victim’s data. It overwrites the MBR and blocks the user’s system, effectively depriving the victim of access to the PC. At this stage, the user sees a ransom demand message and information that his data is encrypted. It is unlikely he would immediately think that he needs to check if someone has stolen his passwords.
According to the analysis of the SentinelOne company, information security expert Vitaliy Kremez and Bleeping Computer, this malware also contains a code for erasing files from the victim’s machine, but this code was not active at the time of the malware investigation. A second version of the same threat was spotted by G DATA expert Carsten Khan two weeks later.
In sum, Coronavirus is a serious problem when we talk about cybersecurity. Email spammers used COVID-19 to convince people to download malicious attachments. Other fraudsters have set up tens of thousands of websites with pandemic domain names. There are also applications and programs that attack computers and smartphones. We also can’t forget about fraudulent SMSs. So in this period we should pay more attention that before to guarantee the safety of our devices.




