New Bluetooth vulnerability affects over one billion device
PhonesWednesday, 08 September 2021 at 08:11

Cybersecurity researchers have identified a new vulnerability affecting Bluetooth modules. They estimate that this security issue threatens more than a billion devices running Android and Windows. The malware is available in the firmware of Bluetooth chips of Qualcomm, Silicon Labs, Intel and others.
According to MSPoweruser, the vulnerability is available in the firmware of eleven manufacturers of Bluetooth chips. They call the exploit itself "BrakTooth" and so far only three vendors have released patches to protect against future hacks: BluTrum, Expressif and Infineon. The rest of them, including Intel and Qualcomm, have yet to solve this problem; which means that millions of devices remain unprotected.
Also, since jailbreaking requires Bluetooth to be enabled on the device, users are advised to disable Bluetooth as a reliable precaution until all firmware patches have been released by the respective manufacturers.
Products we know that is in use for the Braktooth include (there are others):
-Smartphones - Pocophone F1 , Oppo Reno 5G, etc.
-Dell laptops - Optiplex, Alienware, etc .;
-Microsoft Surface devices - Surface Go 2, Surface Pro 7, Surface Book 3, etc.
-Dell laptops - Optiplex, Alienware, etc .;
-Microsoft Surface devices - Surface Go 2, Surface Pro 7, Surface Book 3, etc.
Bluetooth vulnerabilities are nothing new; as many hackers in the past have used this method to gain illegal access to Bluetooth-enabled devices in order to eavesdrop, steal data, infect with malicious software, or even take complete control of the device.
All the vulnerabilities
Full technical details and explanations for all 16 vulnerabilities can be found on the dedicated BrakTooth website where they are numbered V1 – V16 along with the associated CVEs. The researchers claim that all 11 vendors were notified about these security issues months ago (more than 90 days), well before they published their findings.
Expressif (pdf), Infineon, and Bluetrum have released patches. Despite having received the necessary information; the other vendors acknowledged the researchers’ findings but could not confirm a definite release date for a security patch; citing internal investigations into how each of the BrakTooth bugs impacted their software stacks and product portfolios. Texas Instruments said they would not be addressing the flaws impacting their chipsets.
CVE-2021-28139
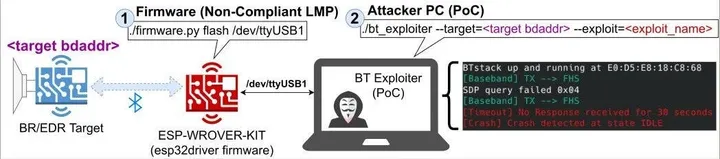
The computers that has the security flaws are available in the Common Vulnerabilities and Exposures (CVE) database. Its goal is to make it easier to share data across separate vulnerability capabilities (tools, databases, and services). The most serious vulnerability in BrakTooth has been listed under CVE-2021-28139, which allows attackers in radio range to trigger arbitrary code execution with a specially crafted payload.
While CVE-2021-28139 is affecting smart devices and industrial equipment running on Espressif Systems’ ESP32 SoC boards, the issue may impact many of the other 1,400 commercial products that are likely to have reused the same Bluetooth software stack.
Loading






