For years, the computer storage segment has been dominated by Hard Disk Drives. This changed abruptly with the rise of affordable and super-fast SSDs (Solid State Drive). For starters, a Hard Disk Drive (HD or HDD) is a non-volatile data storage device. It is installed internally in a computer, and attached to the disk controller of the computer’s motherboard. The HDD was made of a set of mechanical components. It had platters housed inside of an air-sealed casing. The data is written to the platters using a magnetic heard, rapidly moving over spinning platters. A complex system that lasted for years but was full of limitations. With slow reading and writing speeds, and due to its mechanical components, it is very fragile. SSDs have evolved to overcome these limitations and continue to improve with new technology.
Unlike HDDs, SSDs don’t have any kind of mechanical part. They have NAND-based flash memory to store data, everything is, simply put, “digital” and there is no mechanical part. SSDs are faster, more reliable, and more energy-efficient than traditional HDDs. When launched, they were much more expensive than conventional HDDs. However, in recent years, SSDs became way more accessible and the technology evolution brought diversity and improvements. The market currently has various types of SSDs such as SATA, SAS, PCIe, and NVMe.
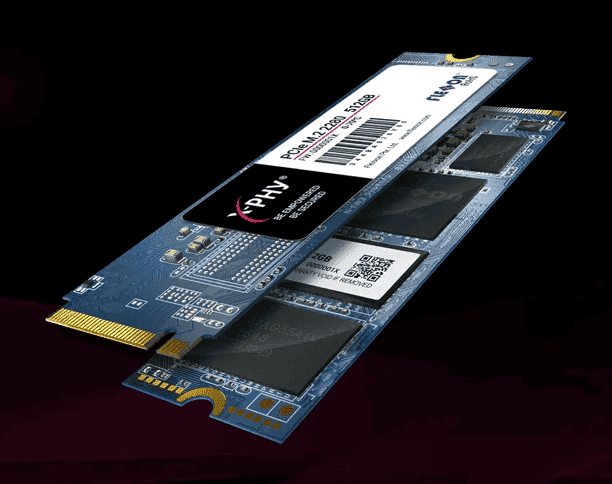
Flexxon’s X-PHY tech is a significant advancement in hardware-based security for SSDs
The latter is one of the fastest and more reliable standards. With the price-per-GB of SSDs dropping, it is likely that they will eventually replace traditional HDDs. With the domain of SSDs, it’s natural to see some concerns raising. How these devices are truly reliable, and how secure they can be to future concerns like cyberattacks? Can I store my precious files on those drives? There is a firm particularly concerned with the security of SSDs – Flexxon.

As tech continues to evolve, cyber-attacks will go at the same pace. Hackers improve their systems and explore every tidbit of hardware to steal users’ data. The damage is massive when the target is a firm with sensitive data. Of Course, despite all the feats made over HDDs, SSDs are still vulnerable to certain things. That’s where Flexxon tries to be different in this segment. In 2021, the firm launched the AI-powered X-PHY SSD tech. It fills some gaps in hardware-based security and reinforces “security by design” by protecting some assets at the physical layer.
About Flexxon
To those unaware, Flexxon is a leading brand that designs, manufactures, and retails industrial NAND flash storage and memory devices. The firm’s key emphasis is to provide top-notch memory solutions that ensure the highest level of data security. The firm has a wide range of memory storage solutions to serve every sector. Flexxon focuses on Cybersecurity, Industrial, Medical, and Automotive (CIMA) applications.

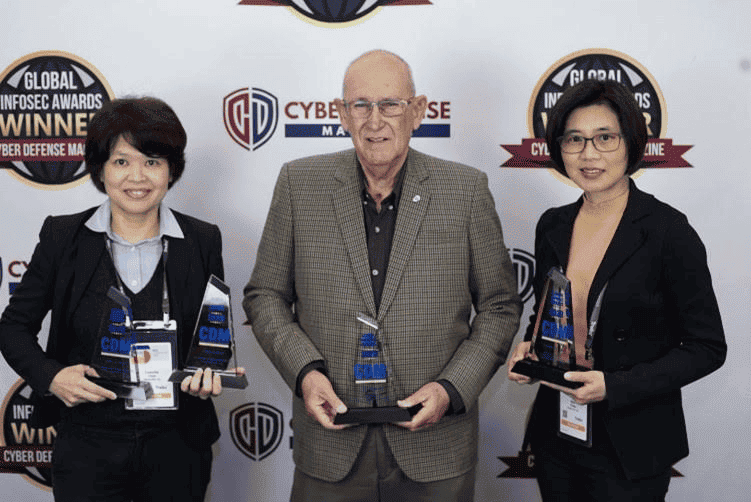
In this article, we’re interviewing Camellia Chan who gives us more details about the firm’s view on the storage segment. She also tells us how innovative their SSDs are and how they have valuable tech. Moreover, we will learn details about Flexxon’s history. Also get some insights on how cybersecurity professionals can improve their security arsenal to protect employee devices and company data.
Interviewing, Camellia Chan, CEO and Founder of Flexxon
- What is the story behind Flexxon? Could you tell us more about Flexxon and its vision?
“Headquartered in Singapore, Flexxon was founded in 2007. It was focused on providing highly reliable, long-lasting and effective data storage solutions. Today, Flexxon is a global firm with a presence in Asia-Pacific, Europe, North America, and the Middle East.
Leveraging on our expertise in industrial NAND flash storage devices, we diversified into the cybersecurity industry in 2019. In 2021, we unveiled the world’s first hardware-based cybersecurity solution for data protection – the X-PHY Cybersecure SSD.
Our very simple vision is to protect the basic rights of digital citizens. As cyberthreats continue to evolve in complexity and volume, I believe our work serves a very important purpose in keeping a step ahead of cyber attackers. Conquering cyber threats then opens up even more possibilities for citizens of the digital age to innovate how we live online.
At Flexxon, we firmly believe that physical layer protection will be the next generation of cyber defense. We also believe that hardware layer cybersecurity is a critical blind spot in too many organizations’ security postures. To be truly effective, the solution must remove the human error element. Also be proactive, hardware-based, and work on a zero-trust framework. The digital landscape is complex, multi-layered and unknown cyberthreats are lurking in every corner. My mission is not only to mitigate cyber threats, but also to prohibit cyber threats.”
-
Can you tell us some details about the X-PHY SSD origin? How it came to be?
“The development of X-PHY was the logical next step in our ongoing mission to lock down the defenses of the physical layer of computing – which we have observed to be a gaping vulnerability in many organizations’ security postures. Our customers, both MNCs and smaller localized organizations, constantly brought up concerns over data security and the rising threat of ransomware, and we knew that this was an issue that desperately needed to be addressed.
The business world has developed an overdependence on software solutions for cybersecurity. But while the software layers do play an important part, leaving a gap in the hardware renders those efforts deficient. What worked twenty years ago cannot keep up with the sophistication and ingenuity of cybercriminals today.
I am proud of our exceptional R&D team who have designed the world’s first AI-embedded firmware-based cybersecurity solution. An invention that now holds over 30 international patents! And has already secured partnerships with major PC companies like Lenovo, ASUS and HP.
Additionally, a big driver for Flexxon is taking human error out of the cybersecurity equation. The AI programming within the firmware of the SSD is designed to remove the reliance on human intervention, by proactively responding to suspicious inbound and outbound data streams without the need for any updating. With X-PHY technology, organizations get 24/7 real-time threat surveillance, with the AI detecting anomalies in regular data access patterns, such as malware, ransomware attacks and data cloning; and deploy hardware sensors to fend off physical intrusions such as side channel attacks.”
-
Can you give us more details about the rapid purging features and tech?
“The inclusion of the rapid purge feature is an essential safety net, because no provider should be able to claim 100% effectiveness in keeping all cyberattacks out.
With the rapid purge feature, users have the option of immediately destroying private, confidential, or classified information if it falls in the wrong hands – a capability that is particularly important in security critical industries.
A great example of the benefits of rapid purging can be tied to the FBI’s recent warning against using public charging stations. This comes as a result of criminals exploiting charging stations and loading malware onto public USB charging stations to maliciously access electronic devices while they are being charged. Now that remote work is standard, employees may be using public sharing stations unbeknownst to them of the dangers that lurk.
Organizations must suit up company owned technology security, such as laptops, to avoid sensitive information from being exposed and greater consequences – this is where rapid purging can come into play. When a computer or other work asset that contains sensitive data is under threat, rapid purging can be used to quickly destroy confidential information ensuring that a cyberbreach can be stopped at a faster rate. This is a particularly important feature to have for industries that handle sensitive and personal information, such as the military and defense sector, healthcare, government agencies and financial services.
While this may seem like the nuclear option, it is important to have this choice to protect organizational data in dire situations.”
-
Can you detail how game-changing is this feature, and why it’s important to expand the security care to the physical layer?
“Traditional cybersecurity efforts are simply not cutting it anymore. Protection at the external layers routinely suffer from the failure to detect threats in a vast external environment and the continued reliance on human intervention to patch and update security protocols.
At the physical layer, the environment is different. All malicious threats are forced to comply with a controlled environment, providing the in-built AI a very clear and specific set of programmed commands to analyze and respond to – as opposed to the external environment where AI needs to contend with signature-based protocols where bad actors can easily disguise themselves and avoid detection.
The difference between deploying AI at the external versus internal layer comes down to the sheer scope of possibilities that need to be assessed – at the hardware layer this is reduced to a very clear set of read-and-write commands which makes it near-impossible for bad actors to hide malicious attacks and bypass security.”
-
Is the X-PHY SSD ready for the new, modern, and complex, cyberattacks?
“X-PHY SSD was designed for new, modern and complex cyberattacks. The very issue with current cybersecurity solutions is that they cannot be designed solely to deal with today’s threats, since cybercriminals are constantly evolving their methods.
Thus, we built the X-PHY on a patented self-learning algorithm. It can detect abnormalities in read-and-write patterns, and identify them as threats. This is a powerful and standout mechanism – by applying this technology, X-PHY SSD is continuously learning and building defenses against complex cyberattacks.
In addition, we are building on the X-PHY’s patented technology and methodologies to create an entire ecosystem of solutions that prioritise data security and protection across a range of applications. We look forward to sharing more updates with you when ready!”
-
Can you tell us how your X-PHY SSD differentiates from the competition? How confident are you regarding its large-scale performance?
“Flexxon’s X-PHY Cybersecure SSD is the world’s first AI-embedded cybersecurity solution for unmatched performance and protection against all cyberattacks. X-PHY Cyber Secure SSD monitors and protects user data in real-time and stops security threats including, system attacks, physical attacks, and ransomware attacks. X-PHY SSD defends against threats by monitoring variances in direct suspicious temperature fluctuations and unusual movements. Important differentiators include X-PHY’s 30 patents, plus, its rapid purging capabilities.
We are confident in its ability to address existing cybersecurity gaps effectively, efficiently, and with easy integration. One hurdle that we face is shifting security mindset when it comes to threat protection as protection at the hardware level is often overlooked. However, as we continue to educate the industry, we are able to navigate this obstacle and noticed that subsequent adoption naturally occurs.”
-
What considerations should cybersecurity professionals include in their security arsenal to protect employee devices and company data?
” Speaking from Flexxon’s area of expertise, a lockdown capability should be inbuilt in the hardware to avoid tampering and physical theft. Shutting down infiltrators before they reach your data core and have the ability to gain access to data.
Security testing for software has to be an industry standard. At the basic level, Static Application Security Testing (SAST) should be deployed to scan and rectify potential vulnerabilities at the early stage of development.
Thorough checks and tests on third-party providers are also imperative. As seen from the numerous breaches that have emerged from third-party service providers. Not only should companies ensure that the credentials of your vendors are up to standard, but they should also utilize tools to scan the entire infrastructure for vulnerabilities. Companies can also do their part to address some of the largest threats to cybersecurity. Namely human error, by utilizing tools to scan for compromised credentials and build in mandatory routine password resets.
To no surprise, we must update software constantly, which is inevitable when cyberthreats are evolving and emerging at such a tremendous speed. However, it is important to note that this is not enough. Even the most conscientious updates will allow for new evolving cyberattacks to slip through. Thus, it is important to complement software protection with defense at the hardware level.
On top of all these considerations, my advice is to review the current approach and allocate some of your resources to the hardware. Hardware-based cybersecurity solutions like the X-PHY take the fight down to a controllable environment. At the closest proximity to your data giving rise to greater response and action times. This final layer will be a non-negotiable element of a holistic cybersecurity plan. Especially if defenses at the external layers fail to keep hackers out.”
Flexxon is on the right way to making SSDs more secure
With the establishment of Solid State Drives (SSD) as the predominant tech, it’s important to know how to be safe with this new technology. Flexxon is definitely investing in powerful security systems and firmware to keep storage safe, regardless of the use scenario.





