Computer security researchers have announced the discovery of a major security breach in Android called StrandHogg (in reference to a Viking war tactic). This breach allowed hackers to develop malware capable of seizing bank IDs and passwords. “We have hard evidence that attackers are exploiting StrandHogg to steal confidential information”. Says Tom Lysemore Hanson, from security firm Promon.
The vulnerability makes it possible for a malicious app to ask for permissions while pretending to be the legitimate app. An attacker can ask for access to any permission, including SMS, photos, microphone, and GPS, allowing them to read messages, view photos, eavesdrop, and track the victim’s movements.
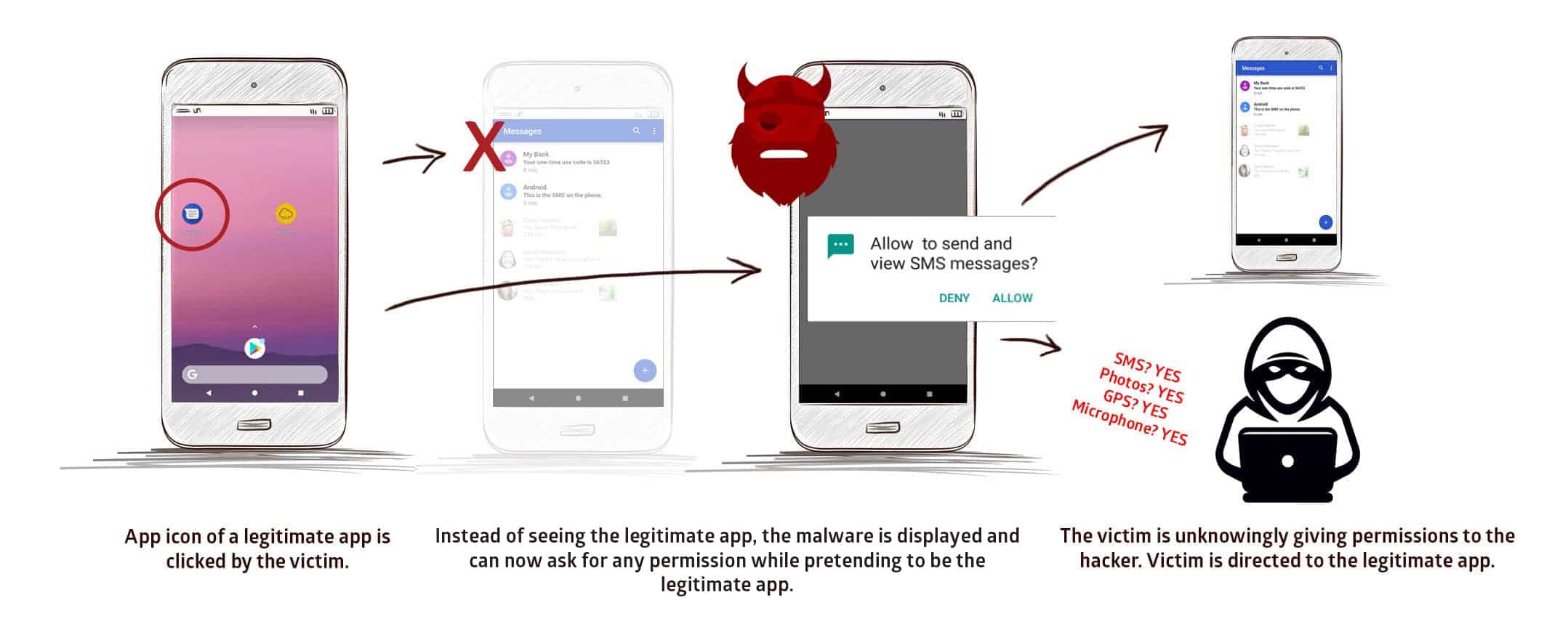
The attacker can request permissions which would be natural for different apps to request, in turn lowering suspicion from victims. Users are unaware that they are giving permission to the hacker and not the authentic app they believe they are using.
By exploiting this vulnerability, a malicious app installed on the device can attack the device and trick it so that when the app icon of a legitimate app is clicked, a malicious version is instead displayed on the user’s screen.
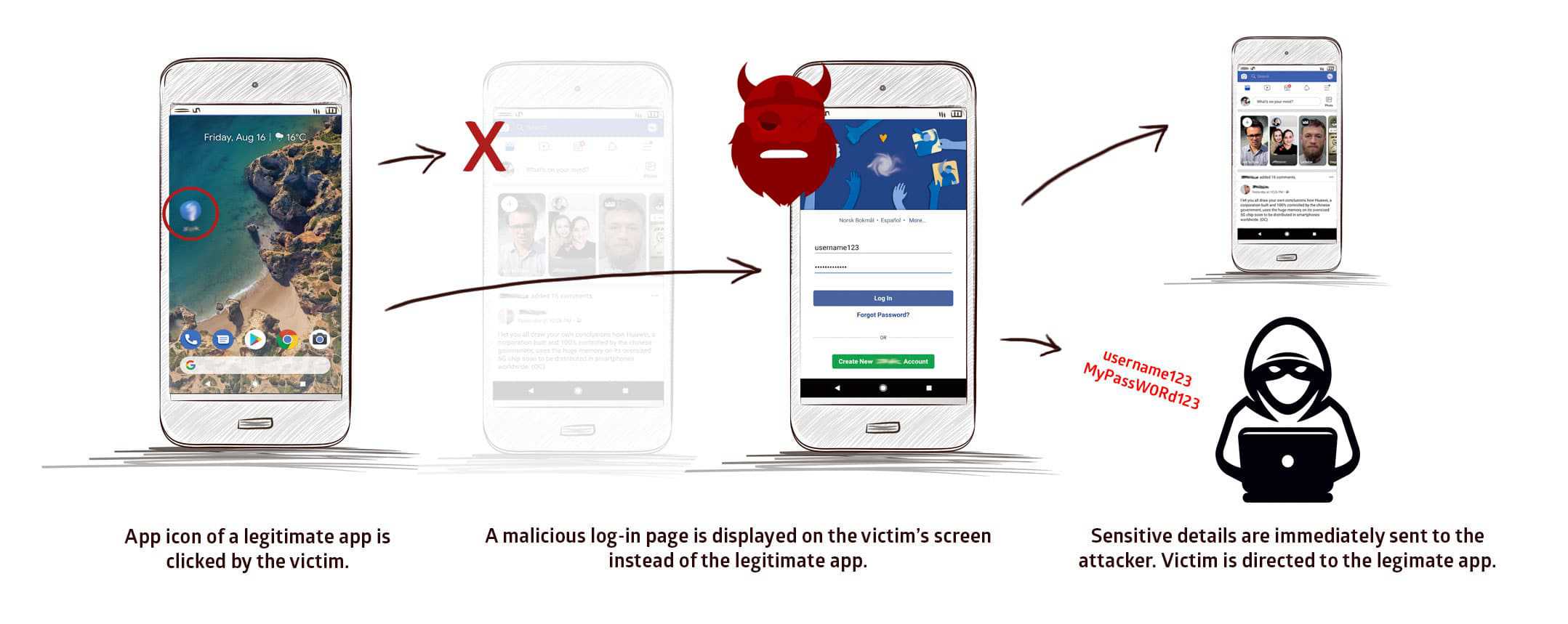
When the victim inputs their login credentials within this interface, sensitive details are immediately sent to the attacker, who can then login to, and control, security-sensitive apps.
What’s the impact?
- All versions of Android affected, incl. Android 10
- All top 500 most popular apps are at risk
- Real-life malware is exploiting the vulnerability
- There are 36 malicious apps exploiting the vulnerability
- The vulnerability does not require root access
When exploited by hackers
- They can listen to the user through the microphone
- Take photos through the camera
- Read and send SMS messages
- Make and/or record phone conversations
- Phish login credentials
- Get access to all private photos and files on the device
- Get location and GPS information
- Access to the contacts list
- Access phone logs
StrandHogg is unique because it enables sophisticated attacks without the need for a device to be rooted. It uses a weakness in the multitasking system of Android to enact powerful attacks that allows malicious apps to masquerade as any other app on the device. This exploit is based on an Android control setting called ‘taskAffinity’. Which allows any app – including malicious ones – to freely assume any identity in the multitasking system they desire.





any way to prevent the attacks??
What are the 36 apps affected?
Give solution