Ian Beer, a member of Project Zero, Google’s working group to find new security vulnerabilities, has published a series of technical articles describing a targeted attack on the iPhone.
These attacks use websites that discreetly has malicious software to collect contacts, images and other data. Google's analysis suggests that websites with these "traps" have thousands of visit times per week.
"There was no target discrimination; simply visiting the hacked site was enough for the exploit server to attack your device, and if it was successful, install a monitoring implant".
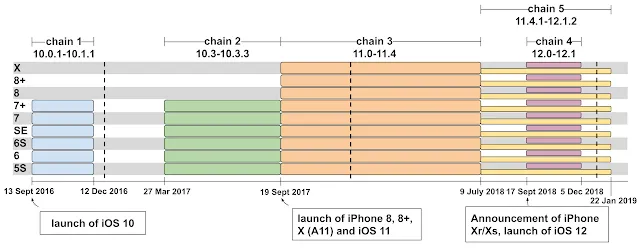
The attackers were using 12 separate security flaws to compromise the devices. Most were bugs in Safari, the default web browser for the iPhone and Apple products.
A very deep dive into iPhone Exploit chains found in the wild
Once inside a person's iPhone, they could access a huge amount of data, including contacts, images and GPS location data. This information could be subject of transmission to an external server every 60 seconds.
To be targeted might mean simply being born in a certain geographic region. Or being part of a certain ethnic group. All that users can do is be conscious of the fact that mass exploitation still exists and behave accordingly. Treating their mobile devices as both integral to their modern lives. Yet also as devices which when compromised, can upload their every action into a database to potentially be used against them.
The implant was also able to collect data from applications that a person was using. Such as Instagram, WhatsApp and Telegram. The attackers were able to attack "almost all versions, from iOS 10 to the latest version of iOS 12".
The Google team notified Apple of the vulnerabilities on February 1 of this year. Subsequently, six days later, Apple published a patch to close the vulnerability.
Unlike other security flaws, which simply describe hypothetical uses of vulnerabilities, Google discovered that this attack was being used by cybercriminals.
Loading