Known as xHelper, the Android malware was discovered in 2019 by the cybersecurity specialists Malwarebytes. And it’s pretty resilient, since it even survives a full reset of your device.
xHelper was at the top of Malwarebytes’ detection panels, with more than 33,000 installations. The Californian company was again alerted, in January 2020, by a user whose smartphone had been a victim of the xHelper malware. And whatever she does, the latter has not managed to get rid of it, even by carrying out a factory reset of her mobile.
xHelper: the indestructible Android malware that keeps coming back
Distributed mainly on Android smartphones in the U.S, xHelper works like a backdoor capable of receiving remote commands and installing other applications on the infected device. On its blog, Malwarebytes detailed the journey made by a user of its forum, who was trying to get rid of the bulky malware.
To get rid of xHelper, Amelia removed two variants of the malware. Except that it was back within an hour. So, she went to carry out a factory reset of her device but it did not work also.
An infection involuntarily triggered by Google Play
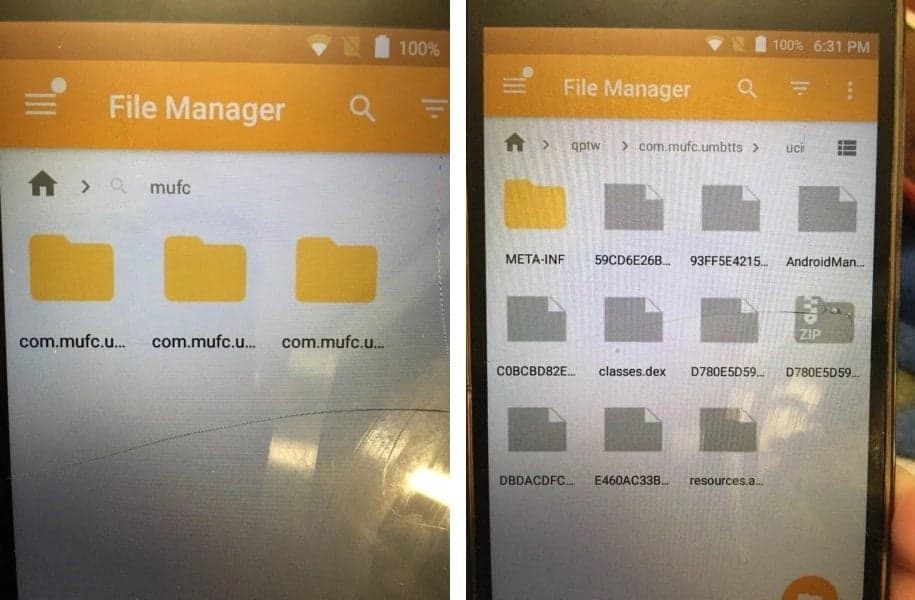
Malwarebytes researchers finally identified the source for systematic reinfection. These are folders in the phone containing files which once executed, install xHelper. Cybersecurity specialists have understood that even if you completely reset your device, these files do not disappear.
The team discovered another Android application package (APK) hidden in the com.mufc.umbtts directory. The APK in question is not a Trojan horse strictly speaking but a “dropper” whose name is Android/Trojan.Dropper.xHelper. VRW. The APK installs a variant of xHelper on the smartphone, which could be triggered unintentionally by an element of Google Play. So the mystery remains.
Either way, to get rid of malware, users need to delete some directories and files and deactivate Google Play first. The files in question differ from one device to another which makes it difficult to identify it and delete it.