Researcher found a security vulnerability with "Apple Login" option
AppleSunday, 31 May 2020 at 13:17
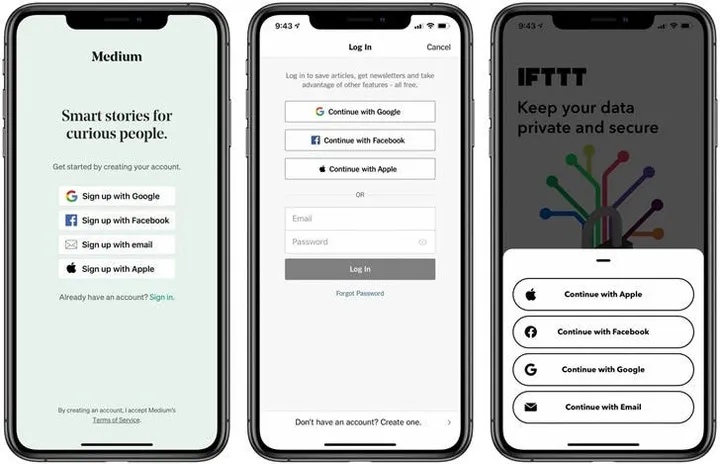
According to recent reports, the researcher Bhavuk Jain has just discovered a serious vulnerability with the "Apple Login" option in April. Apparently, the security flaw allows malicious hackers to take users' accounts. However, this vulnerability seems to be specific to third-party applications that are using the "login with Apple" feature. It affects applications that haven't implemented other security measures.
Jain states that the "Logging in with Apple" authenticates users through JWT (JSON Web Token). As a result, Apple provides users with the option to share the email tied to their Apple ID or private e-mail address. This will create a JWT for logging in the user. According to the report, JWT for Apple ID email and the signature of the token was verified using Apple's public key. If the error has not been found, malicious users could create a JWT and use it to access a person's account.
In an interview with The Hacker News, Jain talked about the severity of this vulnerability:
"The impact of this vulnerability is critical. After all, it may allow a full account to take over. Many developers have integrated "Apple Login" because it is mandatory for applications that support other social logins. Among applications using "Sign in with Apple" feature we can list Dropbox, Spotify, Airbnb, Giphy (now acquired by Facebook)"
The researcher states that Apple is aware of the issue. Upon further inspection, the company concluded that no account was compromised with this method. Moreover, the issue is patched and users can continue to use this login method. According to the company's Apple Security Bounty Program, Jain will receive a $100,000 award for reporting the vulnerability.
Loading