
In an age where smartphones have become an integral part of our lives, ensuring the security of these devices is of paramount importance. Mobile phones are no longer just tools for communication; they hold a treasure trove of personal information, sensitive data, and valuable memories. With the increasing sophistication of cyberattacks, it's crucial to take proactive steps to protect your mobile phone from hackers. This article will provide you with essential insights and practical tips to safeguard your device and your digital life.
Understanding the Threat Landscape
Before diving into the ways to protect your mobile phone from hackers, it's important to understand the various threats you might face:
- Malware and Spyware: These malicious software programs can infect your device through deceptive apps, attachments, or compromised websites, enabling hackers to steal information, monitor your activities, and even control your device remotely.
- Phishing Attacks: Hackers often send fake messages or emails that appear legitimate, tricking you into revealing personal information or clicking on malicious links that can compromise your phone's security.
- Unsecured Wi-Fi Networks: Connecting to unsecured public Wi-Fi networks exposes your device to potential eavesdropping and man-in-the-middle attacks.
- Outdated Software: Failing to update your device's operating system and apps can leave vulnerabilities open for hackers to exploit.
- Physical Access: A lost or stolen phone can provide unauthorized access to sensitive data if it's not adequately protected.
Practical Tips to Protect Your Mobile Phone
1. Use Strong, Unique Passwords and Biometrics:
The first and most crucial step to protect your phone from hackers is to lock it when you're not using it. Set a PIN or passcode to unlock it. Use at least a 6-digit passcode. You can also use your fingerprint, retina, or face to unlock your phone. In addition to locking your phone, also use a string pin or pattern. Enable biometric authentication methods like fingerprint or facial recognition for an additional layer of security.

2. Regularly Update Your Operating System and Apps:
Keep your device's operating system and apps up to date to patch security vulnerabilities. Software updates are essential for the security of your phone. They often include security patches that fix vulnerabilities that hackers can exploit. Therefore, it is crucial to keep your phone's software up to date
3. Be Cautious with App Downloads:
Be careful what you download on your phone. Only download apps from trusted sources like the Apple App Store or Google Play Store. Avoid downloading apps from unknown sources. Also ensure that you read reviews and check app permissions before downloading to ensure they are trustworthy.
4. Install Antivirus and Security Apps:
Anti-malware protection is essential to protect your phone from malware that can steal your sensitive info. Install a reliable mobile security app that can scan for malware, provide real-time protection, and help you locate your device if it's lost. It may also be a good idea to go for one that can keep your mobile phone up to date.
5. Beware of Phishing Attempts:
Be cautious of unsolicited messages, emails, or links, especially asking for personal or financial information.
Verify the sender's identity before clicking on any links or providing information. In fact, when you see links from unknown source, avoid them. In some cases, a simple click of these links can compromise your mobile phone and your personal data can be stolen.
Verify the sender's identity before clicking on any links or providing information. In fact, when you see links from unknown source, avoid them. In some cases, a simple click of these links can compromise your mobile phone and your personal data can be stolen.
6. Use Encrypted Connections:
When browsing, ensure websites use HTTPS encryption, especially when handling sensitive data like passwords or credit card information. When the website is not secured, ensure that you do not access the website. They could cause hackers to gain access to your device.
7. Avoid Unsecured Wi-Fi Networks:
Use Virtual Private Networks (VPNs) when connecting to public Wi-Fi to encrypt your data and protect against eavesdropping. Avoid using unsecured public Wi-Fi networks. These networks are not secure, and hackers can easily intercept your data. If you must use public Wi-Fi, use a virtual private network (VPN) to encrypt your data
8. Enable Remote Tracking and Wiping:
Activate the "Find My Phone" feature or a similar service to remotely track, lock, or wipe your device in case it's lost or stolen.

9. Secure Your Bluetooth and NFC:
Disable Bluetooth and NFC when not in use to prevent unauthorized access and data transfer. When your Bluetooth is but dormant, it opens a link for PC hackers to access the device.
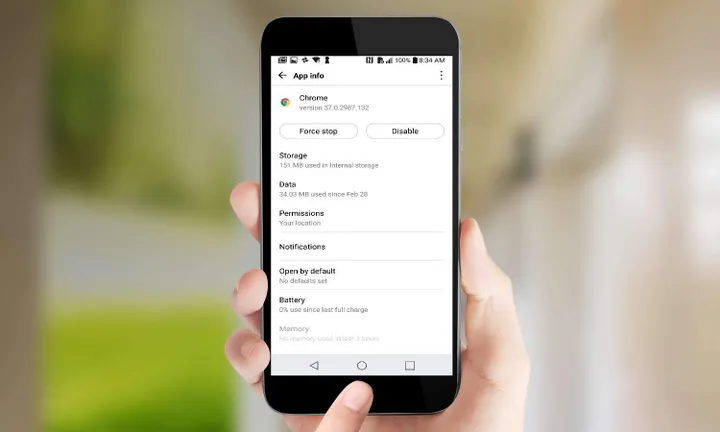
10. Review App Permissions:
Regularly review the permissions granted to your installed apps and revoke any unnecessary access. Also clear your browsing history often, including cookies and cached files. This way, you give hackers as little information as possible to work with if they do break into your phone
11. Use Two-Factor Authentication (2FA):
Enable 2FA for your online accounts whenever possible to add an extra layer of security. When this is active, its gives an extra layer to your device. Hackers can not gain access because they will need a code which will be sent to your email or mobile phone.
12. Educate Yourself:
Stay informed about the latest security threats and best practices to protect your device. This is one of the best ways to protect your device. If you do not know, then you cant protect your mobile phone. Ensure that you use a good number of the tips above and they will go a long way in protecting your mobile phone.
Conclusion
In today's digital age, mobile phones are no longer just chat devices; they are a dairy of the user personal life. They contain info that are private and should not get into the hands of a stranger. To protect your mobile phone from hackers, users will need a couple of actions. Users have to be cautions, use relevant measures as well as staying informed about the latest threats. If the tips in this article are followed, it will reduce the risk of falling victim to hackers.
Popular News
Latest News
Loading



