It's not news to anyone that much of what we do on the internet today end up starting with a Google search, either to find relevant information, to research the price of a product, and even to find new programs, such as browsers. However, this trust in search engines can bring some headaches in specific cases. After all, there is a possibility of flaws in the curation of page indexing and also of displayed ads. This is something that can be corroborated by the case in question here. The latest scam to compromise internet security involves Brave Browser.
According to information released by the folks at ArsTechnica, a remarkably well-crafted scam was recently spotted on Google, using the identity spoofing of the Brave browser site combined with the purchase of an ad to be delivered at the top of the related search page. Starting with what was seen in the search engine, it is possible to observe that the ad points to a domain other than the one officially used by the Brave website (brave.com). They cite a professional clothing trade website called mckelveytees.com and that possibly, was also a victim in that scam. When clicking, the user was directed to intermediate domains until landing on the fake site.
Brave Browser fake website can easily fool careless users
The big problem when talking about the fake site is that it could certainly fool even the most observant user easily. This shows the scammers' care to make fraud more feasible on initial checks. For this, it uses a string that masks the original URL. Instead, it displays a domain similar to Brave's but including an accent on the letter E. However, this is something that will only draw the attention of certain users.
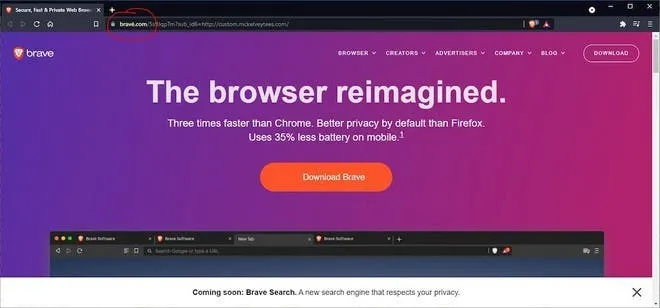
Of course, you might also be wondering about the security certification. The answer is yes, the site also has a valid TLS certificate. It shows the traditional lock for HTTPS access.
The result is that whoever clicked the displayed download button guaranteed access to an installation file. It includes the malware known as ArechClient and SectopRat, embedded in a 303MB ISO inside an executable file. Fortunately, the case in question has already been officially dropped by Google after the signal by Brave and NameCheap. It also included the discontinuity of the malicious domain used to apply the scam.
This case is the latest example of how we need to take care while navigating through the web. Scammers and Hackers are trying to improve their ways to access user data, steal information, and make a profit from it.
Loading